The term “managed service” refers to the management of a company’s entire, or specific parts, of their IT operations. It is the name given to a range of IT services which are provided to a business by a third-party. The third party are specialists in IT and are called Managed Service Providers (or MSPs for short).
Traditionally, IT companies provided support services to companies on an ad-hoc basis, and some still do. Managed services, on the other hand, allows an MSP to implement a system of monitoring and issue resolution. If requested, an MSP would also set up the IT infrastructure in addition to managing it.
What do managed services include?
Typically, managed services comprise the following services:
- Desktop as a Service (DaaS)
- Cybersecurity services or managed security
- Network management
- Identity and Access Management (IDAM)
- Hosting services
- Hardware as a Service
A company can choose to outsource specific parts of their IT setup or the entirety of their IT operation. This purely depends on the company, their IT requirements and the structure they have internally.
Why would a company use an MSP for IT management?
The main reasons why a business would choose an MSP is primarily down to cost-effectiveness and business efficiency. If a company were to invest in setting up their own IT department, the cost of hiring the staff, the hardware and software can be very steep.
With managed services, the costs are known and easy to factor into the budget. A company doesn’t incur any additional cost which is common in the IT industry where upgrades, changes and maintenance can be cost intensive. Users can be added or removed as necessary which gives companies flexibility in costs and ease of expansion.
From a business efficiency perspective, outsourcing IT services allows a company to focus on their business without having to worry about the technical aspects. On the cybersecurity side, an MSP would be able to provide the highest level of security management. MSPs have systems in place to detect malicious threats and keep a company’s systems working.
Finally, MSPs offer round-the-clock technical support which is critical to many businesses in today’s day and age.
How do managed services work? How are they delivered?
Each IT service which is a part of managed service works differently. The process might overlap but the setup, management and maintenance of each service is a standalone project. I will breakdown the process of each managed service in the infographics below.
Desktop as a Service
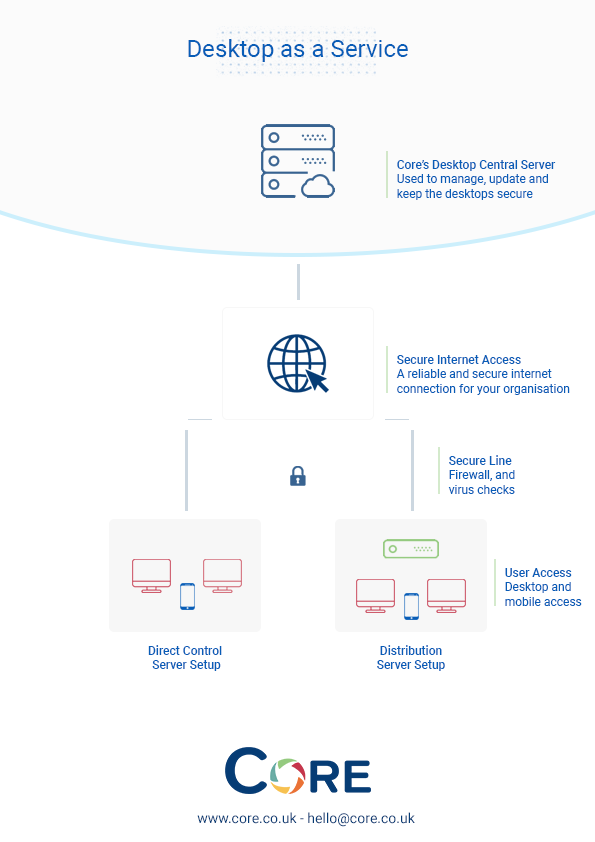
Desktop as a Service is the most commonly outsourced IT service. The process of desktop delivery depends on client requirements. Companies with an internal IT infrastructure will have a server in their office to manage the desktops, while the central server of the MSP directly controls others without an IT department.
When any issues arise with the desktop, there is a desktop management process in place which helps log problems and their resolutions. This increases efficiency in resolving issues and an automated process can be implemented to fix problems.
Some companies provide the hardware to clients which are set up with the relevant operating system and software.
Identity & Access Management (Idam)
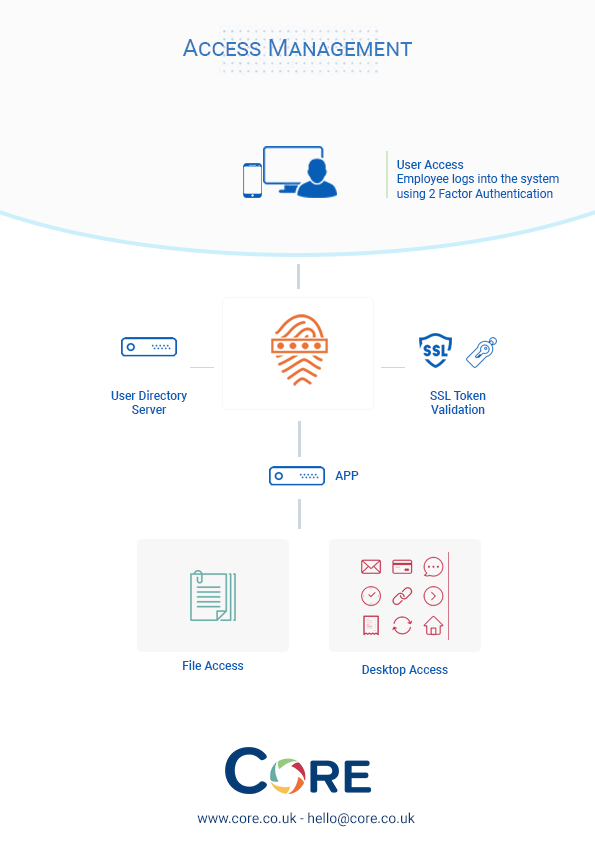
Identity and Access Management (IDAM) requires the setup of a user directory server, which would also have a software setup accessible by the company to grant and revoke permissions to their employees.
The service is very automated, with access being granted by the system, and only permissions need to be set by the relevant person.
Managed Security
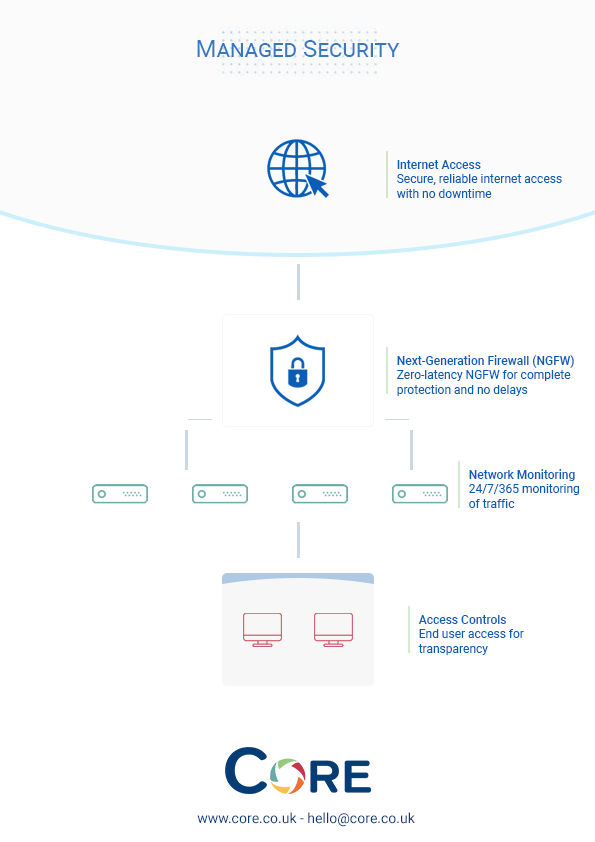
The company’s network traffic is monitored through the security system in place, and threats are resolved to keep the company’s data and systems working.
There are different aspects to cybersecurity such as data protection, access management and virus detection which are all addressed by the cybersecurity team.
Managed Hosting

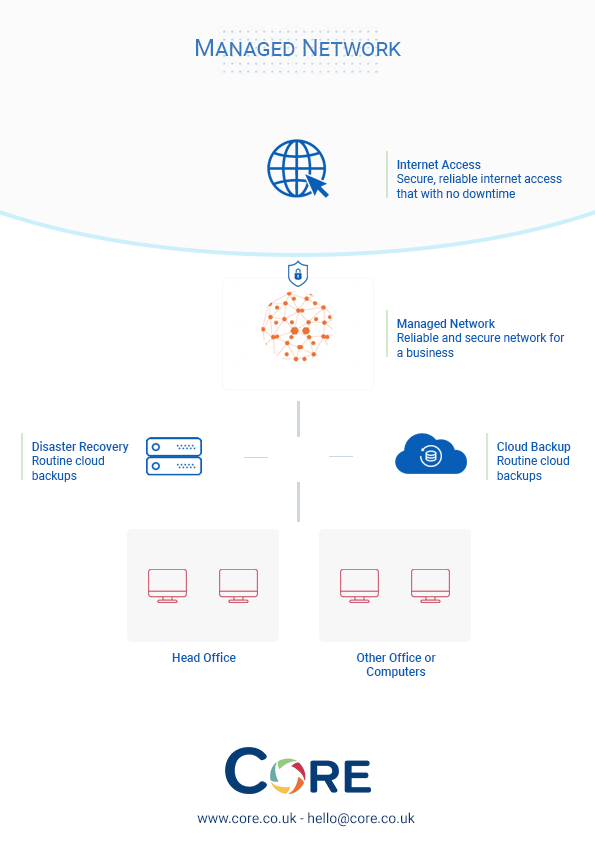
The initial setup of the network (if required) is the most challenging aspect, while the rest of it is heavily automated and allows a business to achieve their network communication goals.
In case of any issues, there are backup facilities and disaster recovery servers setup to keep a companies communication and data secure.
Managed Network
The hosting is set up to custom business requirements allowing a business to be able to access data and files from the server or allow their clients/visitors to be able to gain access to the relevant tools or files.
Hardware as a Service involves providing the clients with the device such as PC/laptops, and anything else required by the company to complete their work.
Some of these services have an overlap, and the setup would be completed together, for example, DaaS would be set up with IDAM and security systems, but different teams are involved in the setup and support for these services.
In addition to the service, the MSP would provide training workshops, guidelines for employees and work with your internal IT team to continue to improve the company’s IT management.